Internet Security - Weaknesses and Targets (WT 2022/23) - t…
A weekly Education podcast
Episodes of Internet Security
Mark All
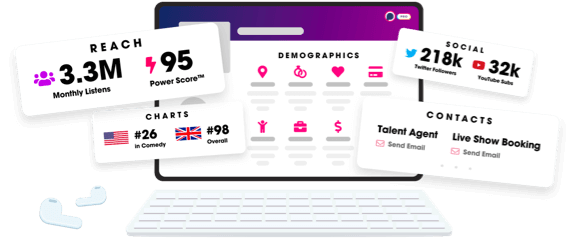
Unlock more with Podchaser Pro
- Audience Insights
- Contact Information
- Demographics
- Charts
- Sponsor History
- and More!
- Account
- Register
- Log In
- Find Friends
- Resources
- Help Center
- Blog
- API
Podchaser is the ultimate destination for podcast data, search, and discovery. Learn More
- © 2024 Podchaser, Inc.
- Privacy Policy
- Terms of Service
- Contact Us
